Anti-tamper security solution for embedded devices Ubiquitous Securus Use secure hardware to prevent data leakage and tampering

Comprehensive technical cooperation and support
In addition to providing security middleware, Ubiquitous Securus comprehensively supports secure network equipment development from consulting before installation to maintenance after shipment of products.
Planning (consulting before introduction)
* Determination of security policy
Confirm the data to be concealed and cooperate in deciding the security policy from the system aspect.
* Selection of hardware
Provision of secret data management utilizing the function of the selected hardware

Design and development (providing library)
* Design and development using hardware
In the case where the hardware has a secure function implemented, design and development taking advantage of the strong hardware security function is implemented.
* Hybrid design and development
Introduction of design of hybrid type with hardware and software and implementation of proprietary cipher unique to software at the design stage.
Production (Providing tools for factory) : option
* Unique encryption tool
Provide tools to securely handle confidential data in production line to prevent information leakage at the time of device manufacturing.
Operation (offer support) : option
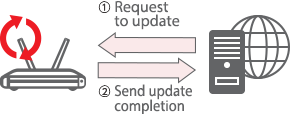
* Secure update
Provide a secure update mechanism to prevent malicious software writing.
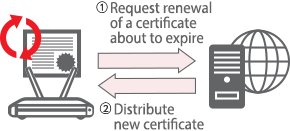
* Update confidential data
Update the certificate at the appropriate timing according to the expiration date of the certificate written to the device.